- Today
- Holidays
- Birthdays
- Reminders
- Cities
- Atlanta
- Austin
- Baltimore
- Berwyn
- Beverly Hills
- Birmingham
- Boston
- Brooklyn
- Buffalo
- Charlotte
- Chicago
- Cincinnati
- Cleveland
- Columbus
- Dallas
- Denver
- Detroit
- Fort Worth
- Houston
- Indianapolis
- Knoxville
- Las Vegas
- Los Angeles
- Louisville
- Madison
- Memphis
- Miami
- Milwaukee
- Minneapolis
- Nashville
- New Orleans
- New York
- Omaha
- Orlando
- Philadelphia
- Phoenix
- Pittsburgh
- Portland
- Raleigh
- Richmond
- Rutherford
- Sacramento
- Salt Lake City
- San Antonio
- San Diego
- San Francisco
- San Jose
- Seattle
- Tampa
- Tucson
- Washington
Two Americans Sentenced for Helping North Korea Obtain Remote IT Jobs
The scheme generated millions for Pyongyang's weapons programs, exposing sensitive data and undermining U.S. economic and national security.
Apr. 16, 2026 at 8:33am
Got story updates? Submit your updates here. ›
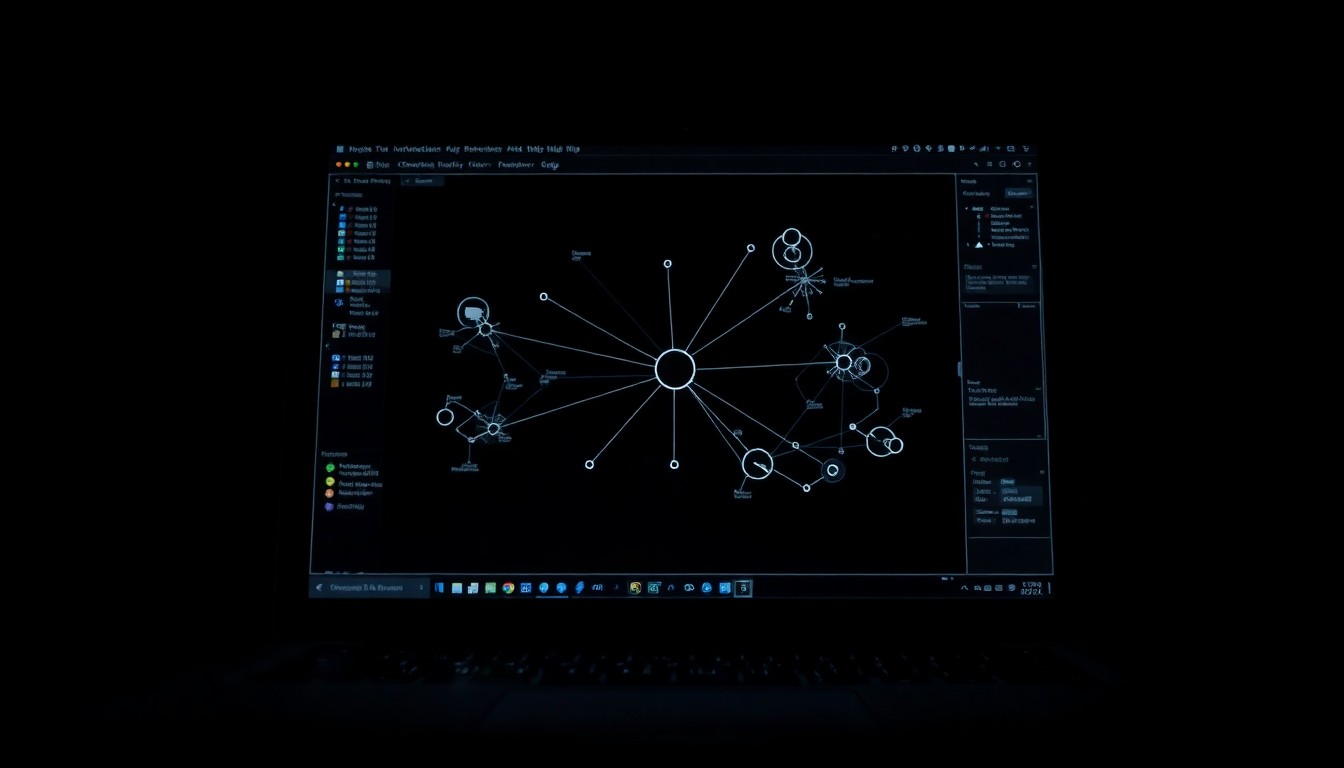 A harsh, close-up view of the complex digital infrastructure that enabled a sophisticated scheme to funnel millions in revenue to a hostile foreign regime.Boston Today
A harsh, close-up view of the complex digital infrastructure that enabled a sophisticated scheme to funnel millions in revenue to a hostile foreign regime.Boston TodayTwo U.S. nationals, Kejia "Tony" Wang and Zhenxing "Danny" Wang, were sentenced to federal prison for helping North Korean operatives obtain remote IT jobs with American companies. The scheme, which ran from 2021 to 2024, used stolen American identities to enable overseas North Korean IT workers to infiltrate over 100 U.S. companies, including Fortune 500 firms and a defense contractor, generating more than $5 million in revenue for the North Korean government.
Why it matters
This case highlights North Korea's increasing reliance on cybercrime and illicit IT work to generate revenue for its weapons programs, as the country faces heavy international sanctions. The scheme exposed sensitive data, including export-controlled information, and caused significant financial losses for the affected U.S. companies, undermining economic and national security.
The details
Kejia Wang, 42, and Zhenxing Wang, 39, both from New Jersey, operated "laptop farms" that made it appear as though the North Korean IT workers were based in the U.S., allowing them to secure jobs using stolen American identities. The scheme exposed sensitive data, including information governed by International Traffic in Arms Regulations, after an overseas co-conspirator accessed systems belonging to a California-based defense contractor.
- The scheme ran from about 2021 through October 2024.
- Kejia Wang traveled to China in 2023 to meet overseas co-conspirators, including a North Korean national.
- The two were charged in June 2025 alongside eight foreign nationals who remain at large and are wanted by the FBI.
The players
Kejia "Tony" Wang
A 42-year-old New Jersey resident who operated "laptop farms" and acted as the U.S.-based manager for the scheme, overseeing multiple facilitators and traveling to China in 2023 to meet with overseas co-conspirators.
Zhenxing "Danny" Wang
A 39-year-old New Jersey resident who was among the facilitators who hosted company laptops and enabled remote access by connecting them to specialized hardware devices.
U.S. Attorney for Massachusetts Leah B. Foley
The U.S. Attorney who stated that the case "exposes a sophisticated scheme that exploited stolen American identities and U.S. companies to generate millions of dollars for a hostile foreign regime."
What they’re saying
“This case exposes a sophisticated scheme that exploited stolen American identities and U.S. companies to generate millions of dollars for a hostile foreign regime.”
— Leah B. Foley, U.S. Attorney for Massachusetts
What’s next
The U.S. State Department has offered a reward of up to $5 million for information on the eight foreign co-conspirators, as well as one suspected North Korean IT worker, that could lead to the disruption of the scheme's financial networks.
The takeaway
This case highlights the growing threat of North Korea's use of cybercrime and illicit IT work to fund its weapons programs, as the country faces heavy international sanctions. It underscores the need for continued vigilance and cooperation between law enforcement, the private sector, and international partners to combat these sophisticated schemes that undermine economic and national security.
Boston top stories
Boston events
Apr. 16, 2026
Rhiannon GiddensApr. 16, 2026
Disney's Beauty and the Beast (Touring)Apr. 16, 2026
An Evening With Shadowgrass (18+)




