- Today
- Holidays
- Birthdays
- Reminders
- Cities
- Atlanta
- Austin
- Baltimore
- Berwyn
- Beverly Hills
- Birmingham
- Boston
- Brooklyn
- Buffalo
- Charlotte
- Chicago
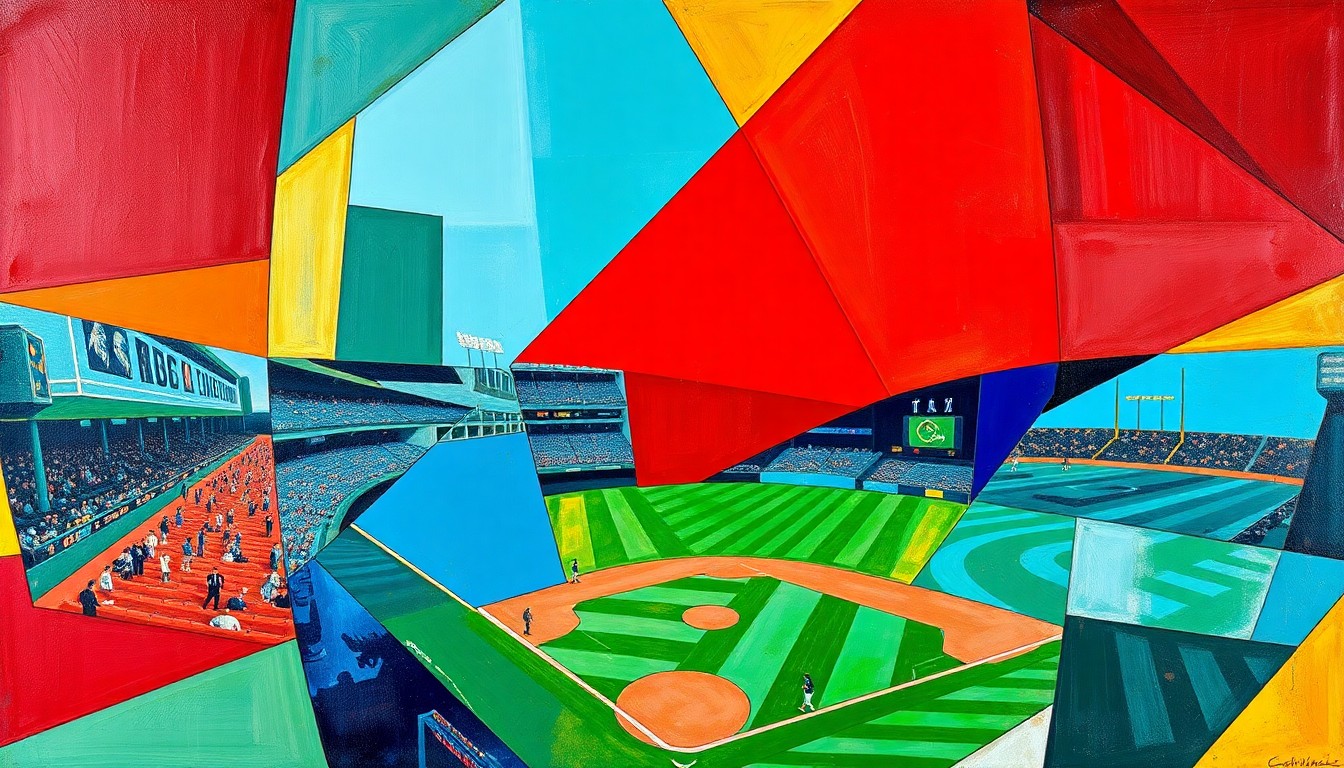
- Cincinnati
- Cleveland
- Columbus
- Dallas
- Denver
- Detroit
- Fort Worth
- Houston
- Indianapolis
- Knoxville
- Las Vegas
- Los Angeles
- Louisville
- Madison
- Memphis
- Miami
- Milwaukee
- Minneapolis
- Nashville
- New Orleans
- New York
- Omaha
- Orlando
- Philadelphia
- Phoenix
- Pittsburgh
- Portland
- Raleigh
- Richmond
- Rutherford
- Sacramento
- Salt Lake City
- San Antonio
- San Diego
- San Francisco
- San Jose
- Seattle
- Tampa
- Tucson
- Washington
Ohio Grapples with AI-Generated Child Porn Amid Legal Gaps
Lawmakers struggle to address the rapid rise of AI-created child sexual abuse materials
Jan. 29, 2026 at 6:15pm
Got story updates? Submit your updates here. ›
The rapid rise of AI-generated child sexual abuse materials (CSAM) is leaving Ohio lawmakers grappling with how to address the issue. Liz Cline, a 15-year-old from Carroll, Ohio, had a photo taken on a family trip that was later used to create deepfake child pornography, highlighting the challenges authorities face in prosecuting these crimes.
Why it matters
The proliferation of AI-generated CSAM poses significant challenges for law enforcement and the legal system, as current laws may not adequately cover these new forms of abuse. This issue raises concerns about privacy, consent, and the exploitation of minors, requiring policymakers to urgently address the legal gaps.
The details
Liz Cline's photo from a family trip was used to create deepfake child pornography, a disturbing example of how AI technology can be misused to produce CSAM. Authorities in Ohio are struggling to prosecute these crimes, as current laws may not cover the unique challenges posed by AI-generated content.
- Liz Cline was a 15-year-old sophomore at Bloom-Carroll High School in 2023 when the incident occurred.
- The photo that was used to create the deepfake CSAM was taken during a family trip to Florida in 2023.
The players
Liz Cline
A 15-year-old from Carroll, Ohio, whose photo was used to create deepfake child pornography.
What’s next
Ohio lawmakers are working to address the legal gaps and develop new policies to combat the rise of AI-generated CSAM, but the issue remains a significant challenge for law enforcement and the justice system.
The takeaway
The proliferation of AI-generated child sexual abuse materials highlights the urgent need for policymakers to update laws and regulations to keep pace with rapidly evolving technology, ensuring the protection of vulnerable minors and the prosecution of those who exploit them.
Cincinnati top stories
Cincinnati events
Apr. 12, 2026
Cincinnati Reds vs. Los Angeles AngelsApr. 12, 2026
Cincinnati Bearcats Mens Baseball vs. Baylor BaseballApr. 12, 2026
Penny & Sparrow